Time to stop complaining about the Defender key fob
On our LR4 I can lock & unlock using the key fob when I'm 100 yards away. Defender range is about 2 feet and sometimes it won't start if the fob is in my left pants pocket instead of my right pocket. I just read on a BMW forum that this is intentional. Land Rover took steps to reduce key fob signal stealing. Some X5 owners have found their vehicles unlocked with items stolen and one owner walked up to a thief inside his X5 and starting it. This was posted on the X5 forum:
The rolljam works by recording and blocking the lock/unlock radio signal from your key fob.
Basically the attacker waits for you to click "open", but they block your fob's signal; you think it didn't work & try again which creates a second signal that is also recorded and blocked.
At this point the attacker has two codes to open your doors, but if they're sneaky they replay the 1st code to unlock or lock the door which you think has now worked ... but now the attacker still has the next code in the sequence which hasn�t yet been expired and they can use any time to unlock the car.
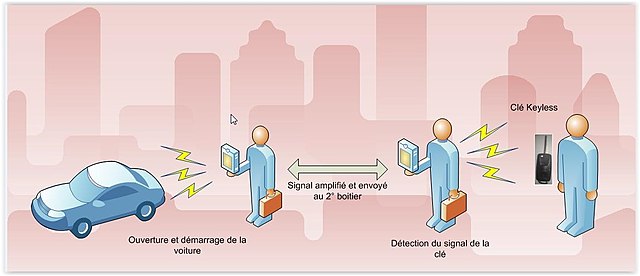
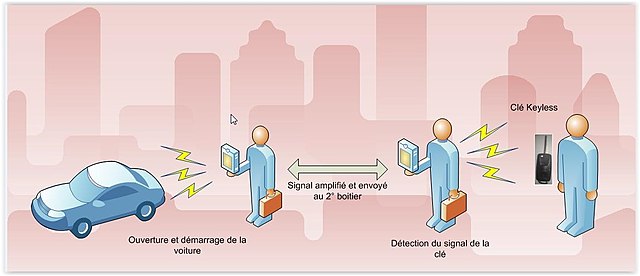
In a relay attack, one attacker gets close enough to your key fob to record its low frequency broadcast - then they broadcast that signal to another attacker who's standing by your car which thinks it's your fob and opens.
The rolljam works by recording and blocking the lock/unlock radio signal from your key fob.
Basically the attacker waits for you to click "open", but they block your fob's signal; you think it didn't work & try again which creates a second signal that is also recorded and blocked.
At this point the attacker has two codes to open your doors, but if they're sneaky they replay the 1st code to unlock or lock the door which you think has now worked ... but now the attacker still has the next code in the sequence which hasn�t yet been expired and they can use any time to unlock the car.
In a relay attack, one attacker gets close enough to your key fob to record its low frequency broadcast - then they broadcast that signal to another attacker who's standing by your car which thinks it's your fob and opens.
In the example mentioned above, the vehicle is programmed to hand out 2 codes and then opens for the owner using the second unblocked code while the sniffer holds on to the first code for later. The first code should be expired upon issuance of the second code. Problem solved.
For proximity, Nextel phones used spread spectrum and hopped frequencies back in 2002 even absent the cellular network. They were very secure.
Ideally, we could move on from these antiquated unsecure keyfobs and switch to a fingerprint start switch with a backup/valet pin code.
I have not had a house key for years and you can't bump my deadbolts because they don't have a keyhole. Why should I have to carry a car key? It's 2021 for Christ's sake.
For proximity, Nextel phones used spread spectrum and hopped frequencies back in 2002 even absent the cellular network. They were very secure.
Ideally, we could move on from these antiquated unsecure keyfobs and switch to a fingerprint start switch with a backup/valet pin code.
I have not had a house key for years and you can't bump my deadbolts because they don't have a keyhole. Why should I have to carry a car key? It's 2021 for Christ's sake.
Last edited by _Allegedly; Aug 28, 2021 at 07:11 PM.
You are correct.
But so am I. If the vehicle expired the first code when it issued the second, the sniffer could then not open the vehicle with the first. Problem still solved.
But so am I. If the vehicle expired the first code when it issued the second, the sniffer could then not open the vehicle with the first. Problem still solved.
You're not understanding what is going on. The system has no idea that the second code was ever issued. They are being intercepted prior to reception.
That was my understanding too. The code is issued by the key fob, not the vehicle.
Encrypted time lapse stamp added to the rolling code would cause the vehicle to expire/reject any codes that were stored and not sent in real time.
The key just has to be able to tell the vehicle when the code was generated in relation to the last code (2.3 seconds later, etc.). When the code is replayed later by the device that recorded it, the vehicle will see that the timing is wrong and reject it.
The key just has to be able to tell the vehicle when the code was generated in relation to the last code (2.3 seconds later, etc.). When the code is replayed later by the device that recorded it, the vehicle will see that the timing is wrong and reject it.


